So far, you can see that the fundamentals behind employing Forms Authentication are easy to manage. In the examples above, the sites are inaccessible until you prove your identity. The example above shows raw authentication with the users and passwords being hard-coded into the Page file. This is useful for illustration. However, in a real application you'll undoubtedly want to assign user identities to various clients visiting your site.
ASP.NET and Visual Studio include facilities for both managing user identities and for managing roles. The following exercise shows how to set up a secure site in which users are allowed access only after they identify themselves correctly.
Create a new Web site named SecureSite. The example included with the CD is a File system Web site so that the site focuses strictly on Forms Authentication. Of course, HTTP Web sites using IIS will also have to go through the IIS authentication process.
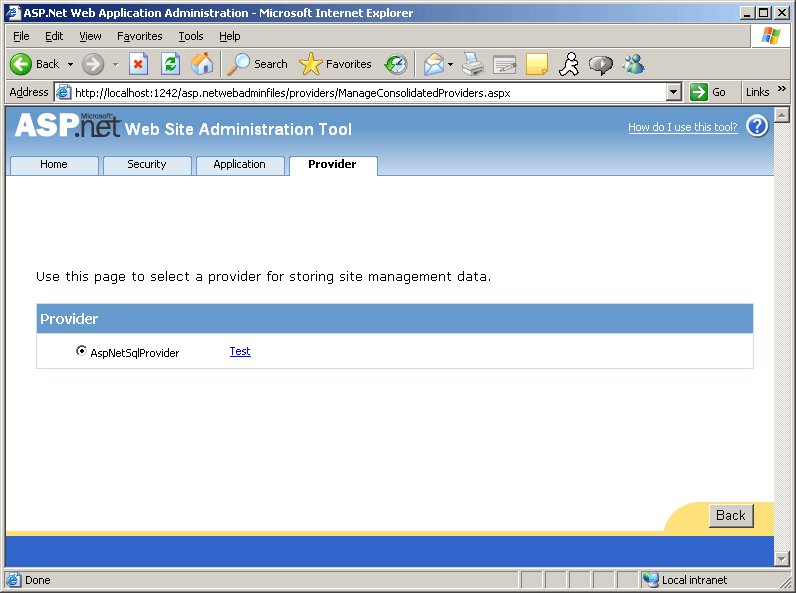
Open the ASP.NET Administration Tool by selecting Web site | ASP.NET Configuration from the main menu. Go to the Provider tab. Select the Select a single provider for all site management data link. Then select AspNetSqlProvider as the provider, as shown here:
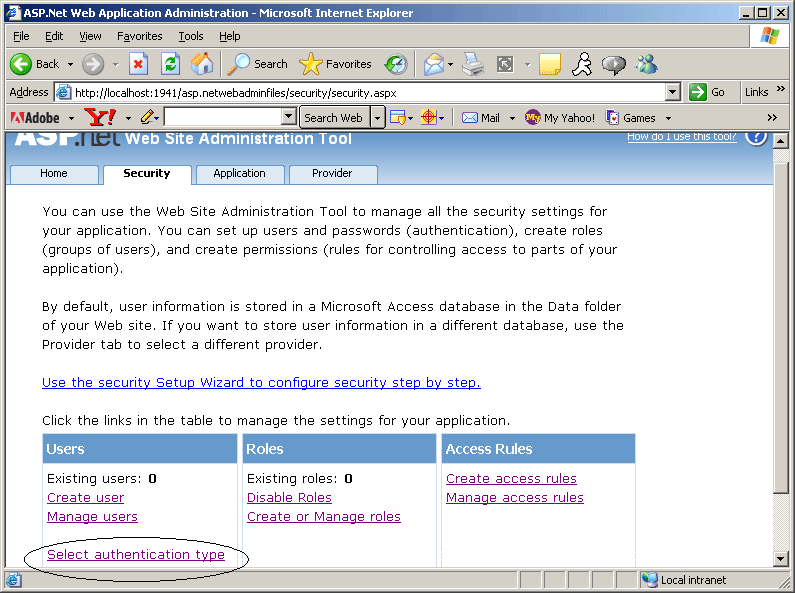
Go to the Security tab. You'll see the page shown in the following graphic. Click the Select authentication type link:
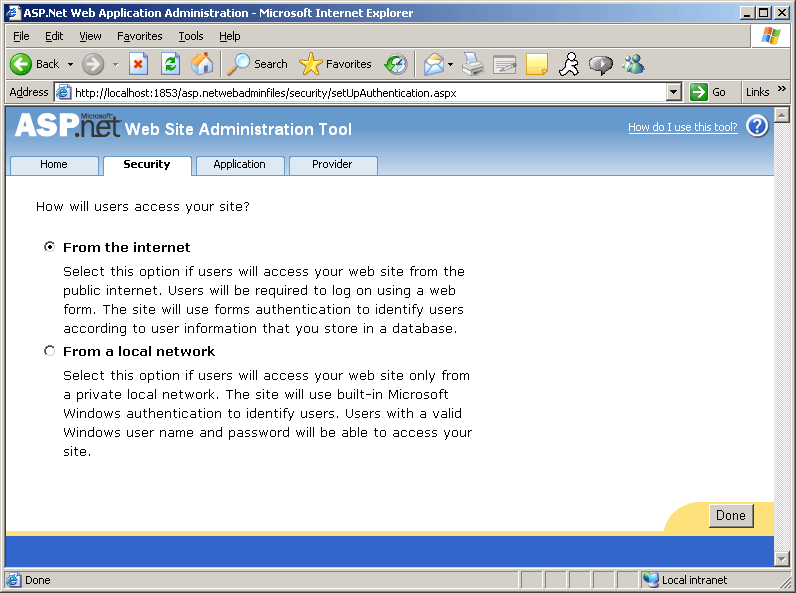
Select From the internet as the access method. This will cause the site to use Forms Authentication.
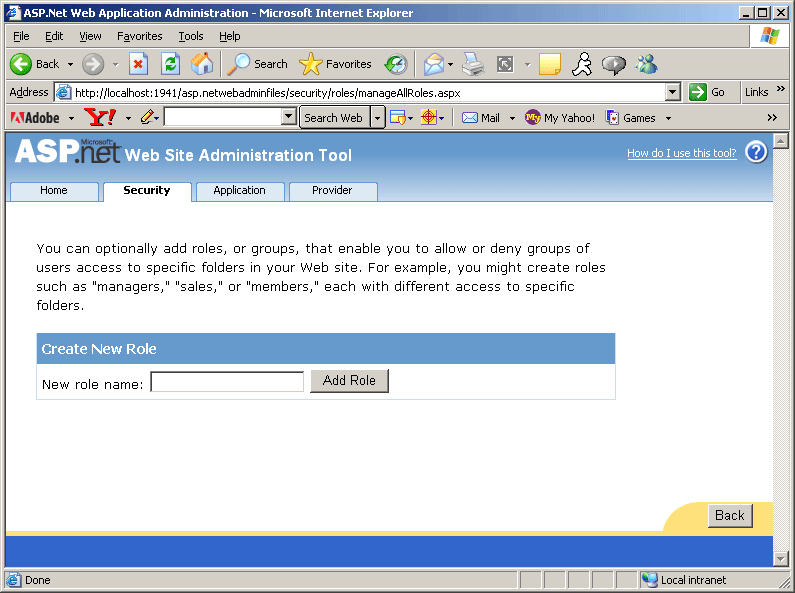
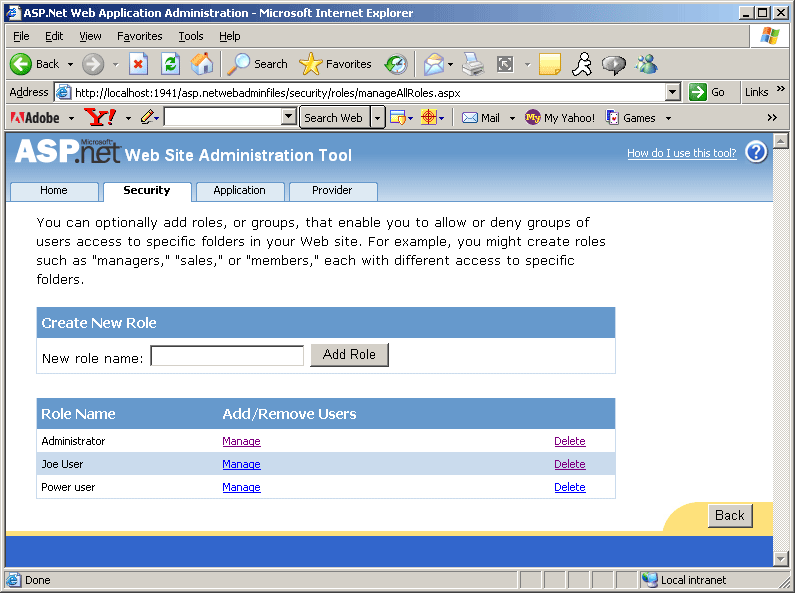
Select Enable Roles and then select Create or manage roles. Add some roles to the site. The example here includes three roles: Administrator, Joe User, and Power user. Add these roles now. We'll assign real users to them shortly.
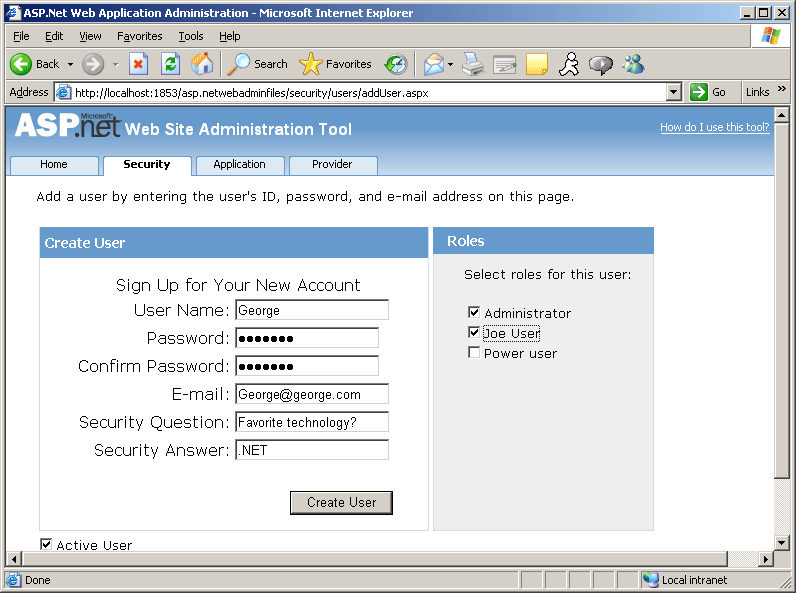
Now add some users and assign some roles. From the main security page, select the Create User link. Add some users. You may assign them to roles now if you wish.
After you've added some users and assigned roles to them, Web.Config should look something like this:
<?xml version="1.0"?>
<configuration xmlns="http://schemas.microsoft.com/.NetConfiguration/v2.0">
<system.web>
<authorization>
<deny users="?" />
<allow roles="Administrator" />
</authorization>
<authentication mode="Forms" />
<roleManager enabled="true"/>
<compilation debug="true"/></system.web>
</configuration>
At this point, you may authenticate users to your site. However, you would probably like to control what parts of your site they may access. To do that, create some access rules. Select the Create Access Rules (on security tab) link to manage authorization. Deny anonymous users, as shown in the following graphic:
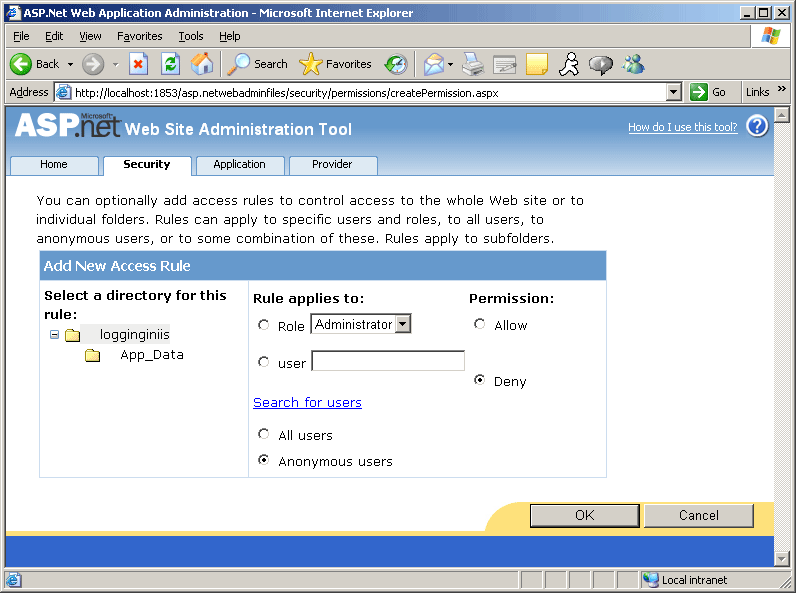
Denying access to anonymous users causes the following changes in Web.Config.
Notice the authorization and the roleManager elements.
<?xml version="1.0" encoding="utf-8"?>
<configuration
xmlns="http://schemas.microsoft.com/.NetConfiguration/v2.0">
<system.web>
<authorization>
<deny users="?" />
</authorization>
<roleManager enabled="true"
defaultProvider="AspNetSqlRoleProvider" />
<authentication mode="Forms" />
</system.web>
</configuration>
Now try running the site. ASP.NET should deny you access to the site, as shown here:
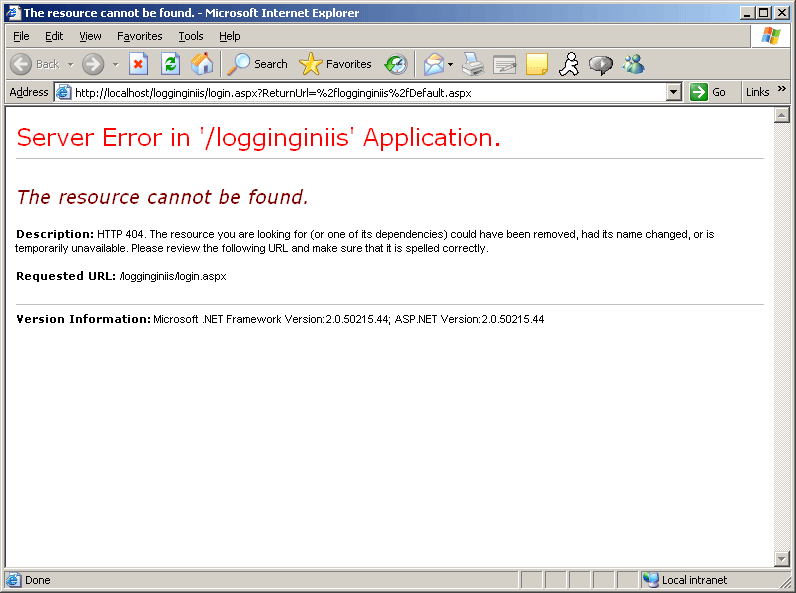
ASP.NET is looking for a way to authenticate the user. However, the site doesn't have one yet. The Forms Authentication setting is set to true, anonymous users are denied access, but there's no instruction to ASP.NET about what to do. There's no login redirect and no login page yet, so ASP.NET simply stops you in your tracks. Let's provide a login page using the ASP.NET login controls.